Table of Contents
From interoperability to smart contracts to decentralized ecosystems to blockchain layers, Web3 is a nerd's wet dream and a newbie's worst nightmare. For many, the blockchain is still a novel concept, but for some, the blockchain is their bread and butter.
If you've ever attended a crypto event or worse still, a developer conference, you'll find yourself swarmed by self-proclaimed Web3 experts who also claim to be the Julian Assanges of decentralized technology.
But yet, the same industry, which is crowded by nerds and tech gurus, is plagued by hacks and scams that even your grandmother would see coming. At least a moderate understanding of technology is required to be granted entry to the Web3 rabbit hole but even the so-called experts seem to be vulnerable to exploits.
Phishing From the Ledger
On Thursday, Ledger suffered a hack that saw $504,000 being stolen from users. At first glance, the Ledger exploit seems to be a complex one. After all, you'd have to get up pretty early to fool those who are so decentralized that only trust cold wallets to protect their assets.
Indeed, the tech jargon was rife in Ledger's explanation of what went down: "The malicious code used a rogue WalletConnect project to reroute funds to a hacker wallet," Ledger explained in a tweet.
"For builders who are developing and interacting with the Ledger Connect Kit code: connect-kit development team on the NPM project are now read-only and can’t directly push the NPM package for safety reasons. We have internally rotated the secrets to publish on Ledger’s GitHub."
FINAL TIMELINE AND UPDATE TO CUSTOMERS:
— Ledger (@Ledger) December 14, 2023
4:49pm CET:
Ledger Connect Kit genuine version 1.1.8 is being propagated now automatically. We recommend waiting 24 hours until using the Ledger Connect Kit again.
The investigation continues, here is the timeline of what we know about…
The Ledger community pointed fingers at an ex-company employee. According to some, a former Ledger staff member accidentally left their email address in the exploit's code.
Breaking: @Ledger @Ledger_Support Here is the guys email jun.sugiura.jp@gmail.com
— MartyParty (@martypartymusic) December 14, 2023
and their twitter handle:@JunichiSugiura
EX - LEDGER EMPLOYEE - I TOLD YOU!!!!
Perhaps this ex-employee was hacked and their gmail used to login to Ledger Github by someone else or they… https://t.co/sP3KKx4phz pic.twitter.com/UBbbYllbbi
However, as complex as the hack seems, it was simply the result of a phishing scam. Ledger claims this former staff member fell for the attack, which opened up access to their NPMJS account.
The exploit compromised dApss with Sushi's CTO Matthew Lilley warning, "Do not interact with ANY dApps until further notice," he tweeted. “It appears that a commonly used web3 connector has been compromised, which allows for injection of malicious code affecting numerous dApps.”
🚨🚨🚨 RED ALERT 🚨🚨🚨:
— I'm Software 🦇🔊 (@MatthewLilley) December 14, 2023
Do not interact with ANY dApps until further notice. It appears that a commonly used web3 connector has been compromised which allows for injection of malicious code affecting numerous dApps.
Essentially, this ex-Ledger Employee, who must have been armed with the technical know-how of the Web3 world, fell victim to nothing more than a phishing attack - the kind you laugh at boomers for falling for.
Gone Phishing
Phishing might be the most basic of internet scams but the simple scam seems to be on the rise in the wonderful world of Web3. As the crypto kool-aid continues to tempt the masses, Web3 converts are realizing how defenseless they are against the centralized banks, traditional financial structures, and the man. But yet, they remain even more defenseless to phishing scams.
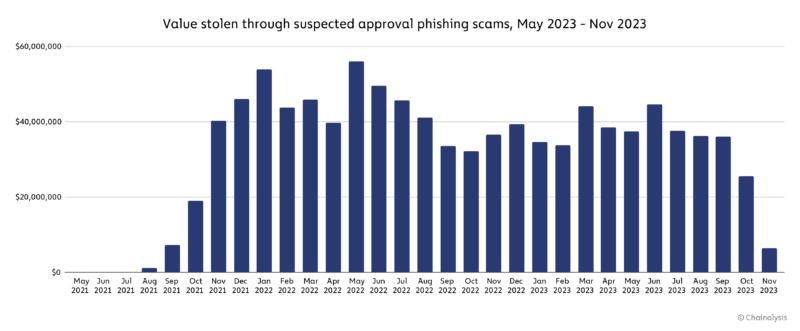
A new report from Chainalysis reveals the "explosive growth" of crypto "approval" phishing scams over the last two years, with at least $374 million stolen this year alone.
The report highlights how "approval" phishing has evolved from phishing in the past. "Typically, scammers trick victims into sending them cryptocurrency, usually through a phony investment opportunity or by impersonating somebody else," the report states.
"But in an approval phishing scam, the scammer tricks the user into signing a malicious blockchain transaction that gives the scammer’s address approval to spend specific tokens inside the victim’s wallet, allowing the scammer to then drain the victim’s address of those tokens at will."
Some victims alone have lost tens of millions of dollars to such scams. Many dAPPs built on smart contract-enabled blockchains require users to approve transactions.
"Approval phishers can take advantage of the fact that many crypto users are used to signing approval transactions — the trick is in what permissions are given, and the trustworthiness of the party receiving that permission," the report states.
This explains why dApps were left vulnerable in the Ledger exploit. Another recent example involved an Inception-level of phishing. Users were warned of a Unisway approval phishing scam (which happened to be fake) and were advised to check their transaction approvals by connecting their wallets to an Etherescan page (which also happened to be fake). Once the user approved their wallet on the page, their funds were drained.
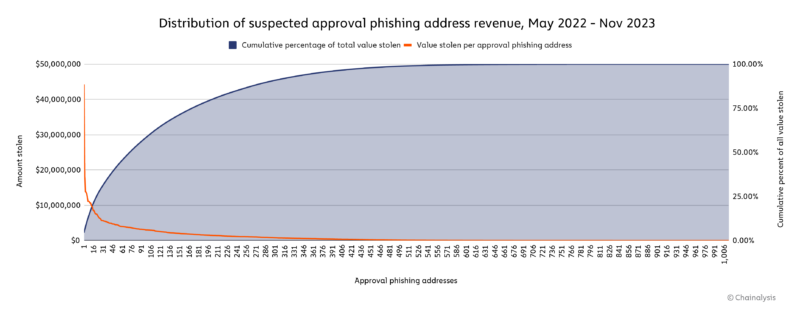
$44.3 million was the most stolen through one phishing address over the last two years. Phishing revenue peaked in May 2022, with victims losing $516.8 million over the year.
Weak Web3
As long as there are computers, there will be cybercrime and as long as there is Web3, there will be exploits. Since the dawn of Web2, hacks and scams prevailed. Despite Web3's so-called revolutionary and disruptive capabilities, there seems to be next to no advancement in security.
Everything has changed with Web3 but also nothing has changed. Even the most decentralized, kool-aid doused degen is vulnerable to exploits.
More worryingly still, the report suggests phishers are targeting victims by "building relationships with them and using tactics associated with romance scams to convince victims to sign approval transactions. "
Romance scams and relationship building with the vulnerable sounds very Web2 to us.
We're not victim-blaming here. The majority of these scammers have built intricate webs of deception, making calculated and malicious moves to subtly but perilously trap the unexpecting.
However, if Web3 is to be the future of finance, technology, whatever, the industry should learn from Web2's past. Sure, just like tax-evading accountants, hackers and scammers will develop new ways to circumvent new layers of protection, but security measures in Web3 are currently far too feable.
Elsewhere